1 Time Use Email: A Complete Guide for 2026
April 14, 2026
In an era where digital privacy concerns dominate headlines and inbox clutter threatens productivity, one solution has emerged as both a blessing and a challenge for businesses and consumers alike. The concept of temporary email addresses has transformed how people approach online interactions, offering a shield against spam whilst simultaneously creating hurdles for legitimate businesses trying to build genuine customer relationships. Understanding this technology is essential for small businesses navigating the complex landscape of email marketing in 2026.
What Is a 1 Time Use Email Address
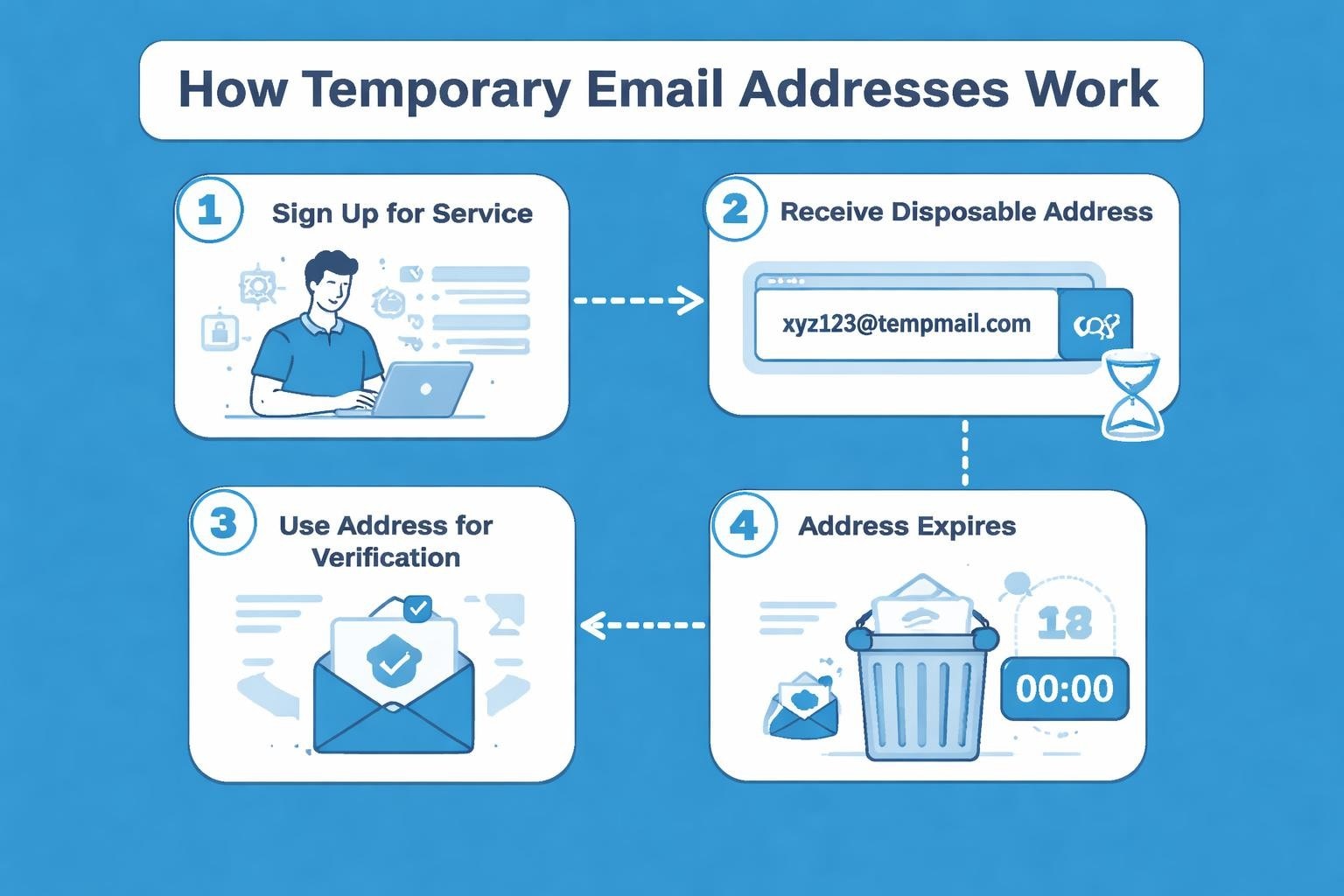
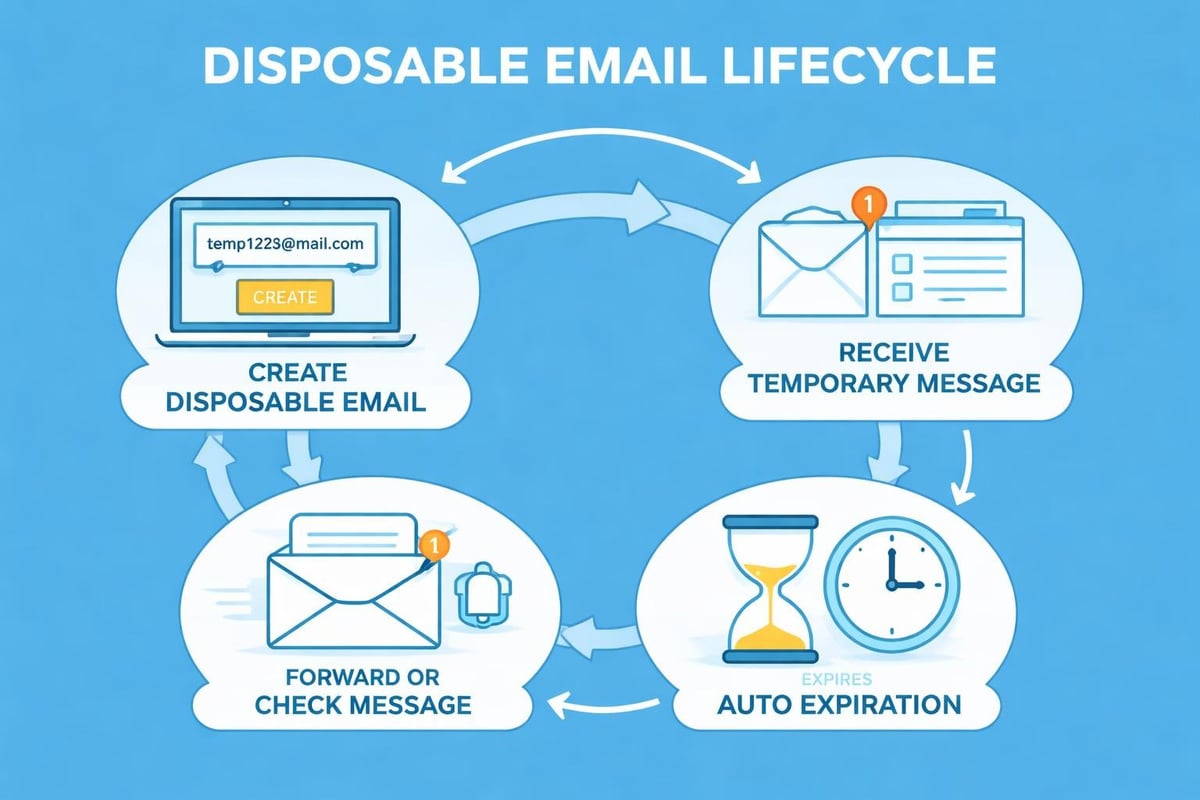
A 1 time use email address is a temporary, self-destructing email account designed for single-use purposes or short-term engagements. Unlike traditional email addresses that remain active indefinitely, these disposable addresses automatically expire after a predetermined period, ranging from a few minutes to several days.
The technology behind these services is straightforward yet powerful. Users visit a temporary email provider's website, receive an automatically generated email address without any registration process, and can immediately use it to sign up for services or receive verification codes. Once the purpose is fulfilled, the address becomes inactive and inaccessible.
Common Applications and Use Cases
People employ 1 time use email solutions across numerous scenarios. Privacy-conscious individuals utilise them when accessing content behind registration walls, downloading free resources, or trying new online services they may not trust fully.
- Online shopping and retail promotions where newsletters are mandatory
- Software trials and beta testing requiring email verification
- Forum registrations for occasional participation
- Contest entries to avoid future marketing communications
- Public Wi-Fi access requiring email authentication
According to research on disposable email addresses, these services gained significant traction as internet users became increasingly aware of data privacy concerns and the monetisation of personal information.
Benefits of Using Temporary Email Services
The advantages of implementing a 1 time use email strategy extend beyond simple spam prevention. For individual users, these services offer substantial protection against identity theft, phishing attempts, and unwanted marketing bombardment.
Privacy Protection and Anonymity
Temporary email addresses create a barrier between your permanent identity and potentially untrustworthy websites. When you provide a disposable address instead of your primary one, you maintain control over who has access to your real contact information. This approach significantly reduces the risk of your email appearing in data breaches or being sold to third-party marketers.
Spam Reduction and Inbox Management
The most immediate benefit is the elimination of long-term spam. When a 1 time use email expires, all future messages to that address simply disappear into the void. This self-cleaning mechanism means you never have to unsubscribe from countless mailing lists or filter through promotional content.
| Benefit Category | Impact | Duration |
|---|---|---|
| Privacy Protection | High | Permanent |
| Spam Reduction | Very High | Immediate |
| Security Enhancement | Moderate | Short-term |
| Convenience | High | Instant |
Security Considerations for Users
Whilst temporary emails offer privacy advantages, they come with security limitations. Most services don't encrypt messages, making them unsuitable for sensitive communications. The security implications of temporary email addresses reveal that these tools work best for low-stakes interactions rather than financial transactions or personal data sharing.
Users should never employ disposable addresses for banking, healthcare, or any service requiring account recovery options. The temporary nature means you lose access to password reset links or important account notifications once the address expires.
Impact on Email Marketing Campaigns
For businesses running email marketing campaigns, 1 time use email addresses represent a significant challenge. These disposable contacts dilute list quality, inflate bounce rates, and distort engagement metrics that inform strategic decisions.
List Quality and Deliverability Issues
When subscribers provide temporary addresses, businesses face immediate and long-term consequences. These addresses typically result in hard bounces after expiration, damaging sender reputation scores with email service providers. As detailed in guidance about email marketing deliverability challenges, even a small percentage of disposable addresses can trigger spam filters and reduce overall campaign effectiveness.
Metrics Affected by Disposable Addresses:
- Open rates become artificially deflated
- Click-through rates fail to represent genuine interest
- Conversion tracking becomes unreliable
- Customer lifetime value calculations skew incorrectly
- List growth metrics appear healthy whilst actual engagement declines
Small businesses using platforms like Astonish Email for their marketing campaigns must implement validation strategies to identify and filter disposable addresses before they contaminate contact databases.
Detection and Prevention Strategies
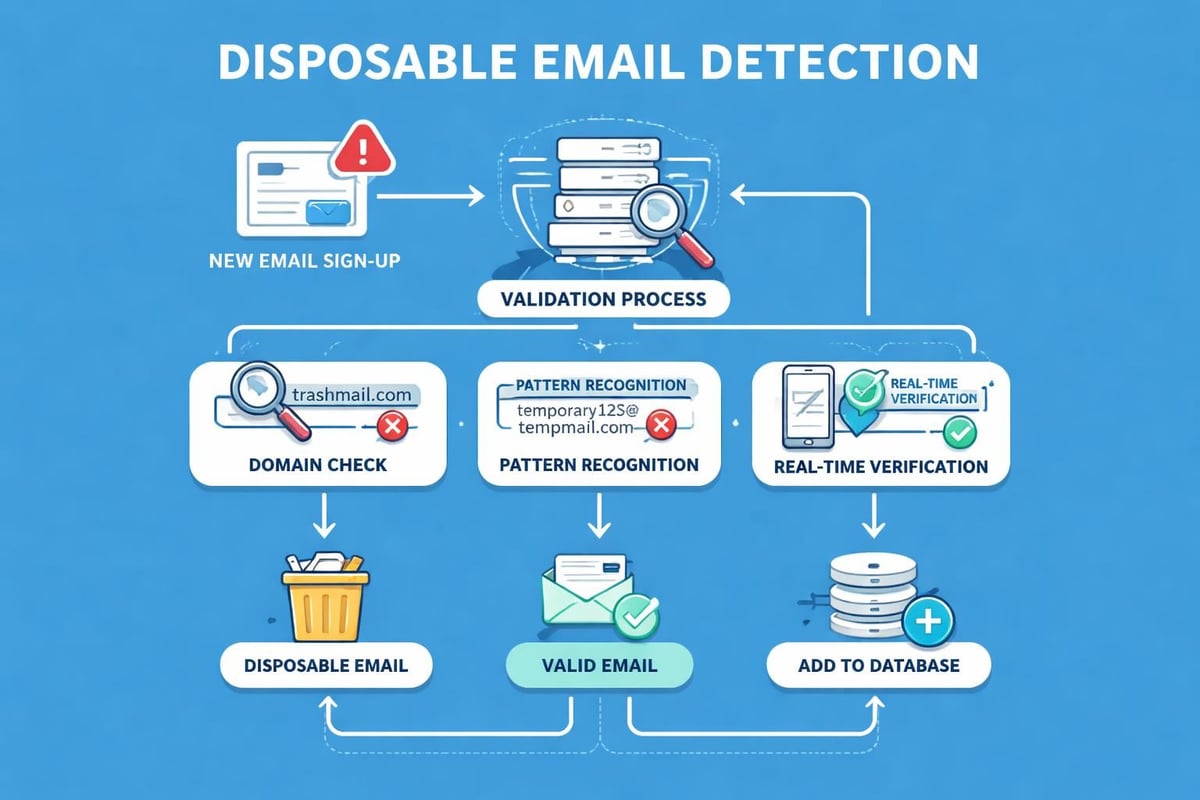
Businesses need robust systems to identify 1 time use email addresses during the signup process. Multiple techniques exist, ranging from simple domain blacklists to sophisticated real-time verification APIs.
Technical Detection Methods
The most basic approach involves maintaining a database of known temporary email domains. Services compile extensive lists of disposable email providers, which businesses can reference during registration. However, new temporary email services launch regularly, making this method require constant updates.
Real-time verification offers more comprehensive protection. These systems analyse email addresses against multiple criteria:
- Domain age and reputation
- Mail server configuration
- Pattern matching against known disposable formats
- Behavioural analysis of signup patterns
- Cross-reference with complaint databases
Advanced detection systems examine syntax patterns common to automatically generated addresses. Many temporary email services use predictable formats that sophisticated algorithms can identify even if the specific domain isn't yet blacklisted.
Balancing Security with User Experience
Whilst blocking disposable addresses protects list quality, overly aggressive filtering can frustrate legitimate users and reduce conversions. Some people genuinely prefer using professional email addresses they create specifically for commercial interactions.
The optimal approach combines automated detection with graduated verification. Rather than outright blocking suspected temporary addresses, businesses can implement additional verification steps like SMS confirmation or social media authentication for these users.
| Strategy | Effectiveness | User Friction | Implementation Cost |
|---|---|---|---|
| Domain Blacklist | Moderate | Low | Low |
| Real-time API | High | Low | Moderate |
| Double Opt-in | Very High | Moderate | Low |
| Multi-factor Verification | Very High | High | High |
Legal and Ethical Considerations
The use of temporary email addresses exists in a complex legal grey area. Whilst creating and using these addresses isn't inherently illegal, certain applications may violate terms of service or specific regulations.
Privacy Laws and Compliance
Data protection regulations like GDPR view email addresses as personal data, requiring businesses to handle them appropriately regardless of whether they're permanent or temporary. The legal implications of using temporary email demonstrate that businesses must maintain the same privacy standards for all collected addresses.
Interestingly, temporary emails can actually support GDPR compliance. The "right to be forgotten" becomes automatic when addresses self-destruct. However, businesses must still provide clear privacy policies and obtain proper consent, even for temporary contacts.
Compliance Requirements:
- Transparent data collection notices
- Clear opt-in mechanisms for marketing
- Accessible unsubscribe options
- Secure data storage regardless of duration
- Proper deletion procedures for expired addresses
When establishing email marketing policies, businesses should address how they handle temporary addresses whilst maintaining compliance across all contact types.
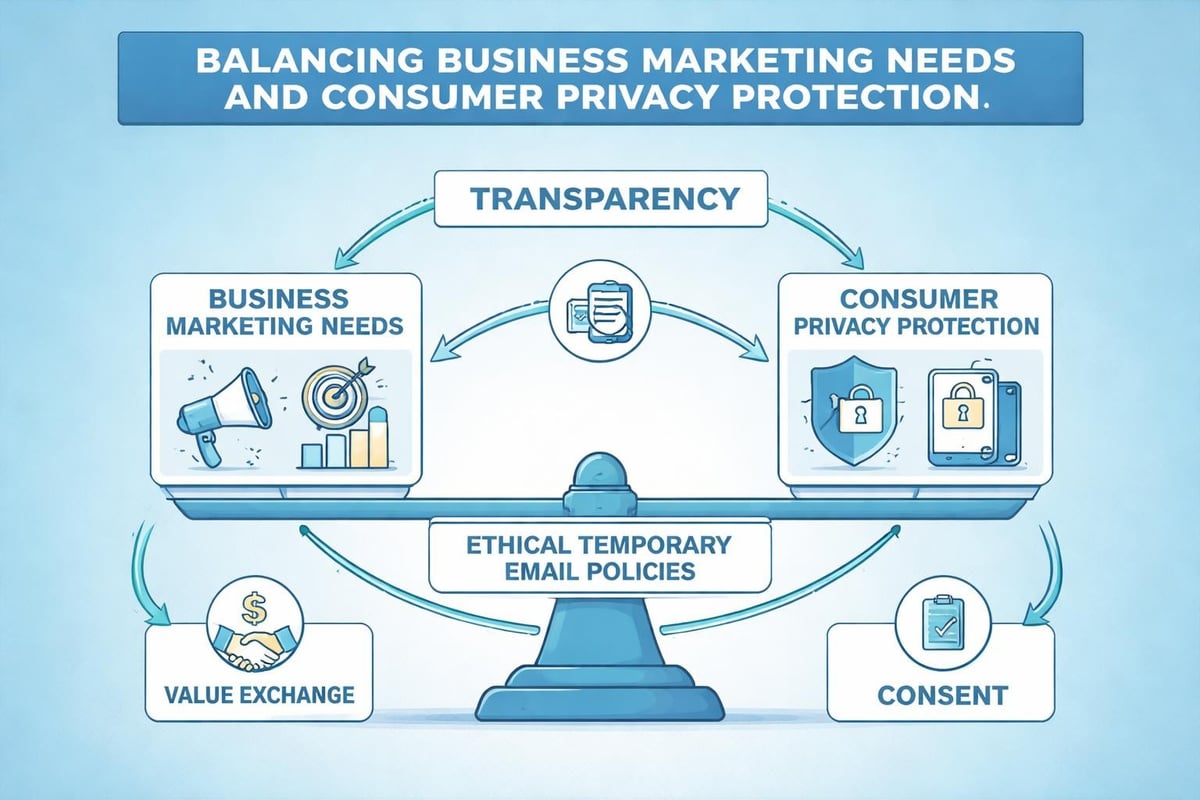
Ethical Marketing Practices
Beyond legal requirements, ethical considerations matter. Aggressive blocking of 1 time use email addresses may exclude privacy-conscious individuals who would genuinely benefit from your products or services. Conversely, knowingly marketing to addresses you suspect are temporary wastes resources and damages sender reputation.
The ethical middle ground involves transparency. Clearly communicate the value subscribers receive in exchange for their email addresses. When the proposition is genuinely valuable, more people provide permanent contact information willingly.
Best Practices for Small Businesses
Small businesses must navigate the temporary email challenge strategically. Resources are limited, making it essential to focus on tactics that deliver the highest return whilst maintaining positive user relationships.
Building Quality Over Quantity
Rather than obsessing over list size, prioritise engagement quality. A smaller list of genuinely interested subscribers using permanent addresses outperforms a massive list contaminated with temporary contacts. Reviews of the best temporary email services show that users comfortable with these tools are sophisticated about privacy, meaning they respond better to respect than manipulation.
Implement value-first strategies that make subscribers want to stay connected:
- Offer exclusive content genuinely unavailable elsewhere
- Provide tools, calculators, or resources solving real problems
- Build community through interactive elements
- Deliver consistent value before requesting any purchase
- Respect inbox space with optimal sending frequency
When building your business email address strategy, ensure your own communications set the standard you expect from subscribers.
Verification and Validation Workflows
Every email collection point should include verification mechanisms. Double opt-in remains the gold standard, requiring subscribers to confirm their address through a link sent to their inbox. This simple step eliminates most temporary addresses whilst improving overall list health.
For businesses concerned about conversion friction, progressive verification offers a compromise. Allow initial access with unverified addresses, but require confirmation before delivering premium content or enabling full account features.
Alternative Solutions and Workarounds
Rather than fighting temporary email usage, innovative businesses are finding ways to accommodate privacy-conscious users whilst still achieving marketing objectives.
Email Aliases and Forwarding Services
Some users prefer alias services over disposable addresses. These tools create unique email addresses that forward to a primary inbox, allowing users to track which businesses share or sell their information whilst maintaining a permanent contact point. Understanding these preferences helps businesses design more appealing signup processes.
Privacy-First Authentication Methods
Forward-thinking companies are exploring authentication methods that don't require email at all. Social login options, phone number verification, and passwordless systems using magic links offer alternatives that respect privacy whilst maintaining security.
| Authentication Method | Privacy Level | User Adoption | Business Value |
|---|---|---|---|
| Traditional Email | Low | Very High | High |
| Temporary Email | Very High | Moderate | Very Low |
| Email Alias | High | Low | Moderate |
| Social Login | Moderate | High | Moderate |
| Phone Number | Low | Moderate | High |
Value Exchange Models
The most effective counter to 1 time use email adoption is creating such compelling value that users willingly provide permanent contact information. When your newsletter delivers consistent insights, exclusive offers, or genuine utility, subscribers actively want to maintain the connection.
Consider tiered access models where basic content remains available to anyone, but premium resources require verified permanent addresses. This approach respects user choice whilst incentivising higher-quality contact information.
Managing Temporary Addresses in Your Database
Even with prevention strategies, some temporary addresses inevitably enter your database. Effective management minimises their impact on campaign performance and sender reputation.
Identification and Segmentation
Create segments specifically for suspected disposable addresses. This allows you to handle these contacts differently, perhaps with shorter nurture sequences or immediate value delivery before the address expires. Monitor these segments for engagement patterns that might indicate legitimate users mistakenly categorised.
Regular list hygiene removes addresses that bounce or show zero engagement. Set automated workflows that archive or delete contacts failing to interact within defined timeframes. This cleanup protects deliverability whilst maintaining focus on responsive subscribers.
Re-engagement Campaigns
Before removing suspected temporary addresses, attempt re-engagement. Some users initially provide disposable addresses but later decide they want ongoing communication. Offering a simple preference update or re-subscription option can convert these contacts into valuable permanent subscribers.
Understanding email contact management best practices helps businesses maintain healthy databases that support both privacy and engagement.
The Future of Temporary Email Services
As we progress through 2026, the landscape of temporary email continues evolving. Enhanced privacy regulations, improved browser privacy features, and growing consumer awareness are shaping how these services develop and how businesses must respond.
Emerging Technologies and Trends
Browser makers are integrating temporary email generation directly into their platforms, making disposable addresses even more accessible. Apple's Hide My Email feature and similar services from other major technology companies normalise this behaviour, particularly among younger, privacy-conscious demographics.
Blockchain-based email systems promise decentralised temporary addresses with enhanced security. These emerging technologies may further complicate traditional email marketing approaches whilst opening new opportunities for innovative businesses.
Adapting Marketing Strategies
The businesses that thrive will view temporary email not as an obstacle but as a signal. Users choosing disposable addresses are telling you something about their trust level and information needs. Savvy marketers respond by building trust first and requesting permanent contact information only after demonstrating value.
Security considerations outlined in temporary email security guides show that as these services improve their security features, they'll attract even broader user bases, making adaptation essential rather than optional.
Integration with Marketing Platforms
Modern email marketing platforms must incorporate sophisticated temporary address detection and handling. The email systems small businesses rely on should offer built-in protection whilst maintaining user experience and conversion optimisation.
Understanding 1 time use email addresses is crucial for small businesses navigating modern email marketing challenges. These temporary solutions reflect growing privacy consciousness and demand more respectful, value-driven approaches to customer communication. By implementing proper detection, focusing on quality engagement, and respecting user privacy preferences, businesses can maintain healthy email lists whilst building genuine customer relationships. Astonish Email provides the tools and guidance small businesses need to navigate these challenges effectively, delivering email marketing solutions that respect both your growth objectives and your subscribers' privacy preferences.